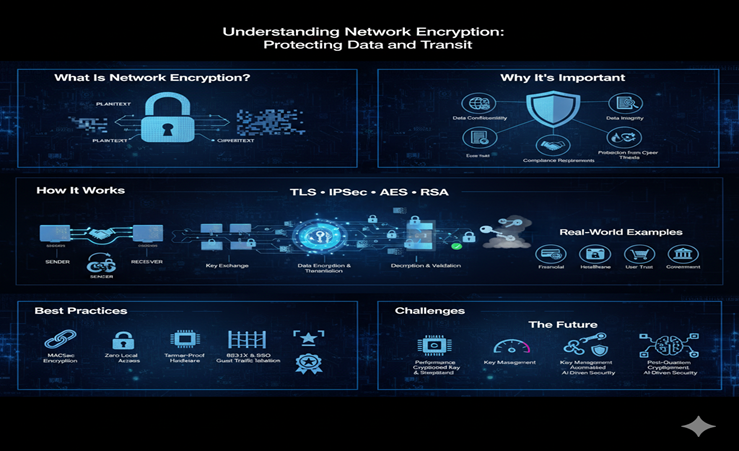
In today’s hyper-connected world, data is constantly flowing across networks—from emails and online payments to video calls and cloud backups. But as this digital traffic increases, so do the risks. Cybercriminals are always looking for opportunities to intercept, steal, or manipulate sensitive data in transit. That’s where network encryption comes into play.
Network encryption acts as a virtual shield, transforming readable information into encoded data that only authorized recipients can decode. It’s the backbone of secure communication on the internet, and it plays a critical role in maintaining privacy, compliance, and trust in digital environments.
Let’s explore what network encryption is, how it works, and why it’s more vital now than ever before.
What Is Network Encryption?
Network encryption is a cybersecurity technique that scrambles data as it moves between devices on a network. Whether you’re sending files within a company’s internal system or transmitting data over the internet, encryption ensures that unauthorized parties can’t make sense of the intercepted content.
The concept is simple: before data leaves its source, it’s transformed into ciphertext using an encryption key. When it reaches its destination, the authorized recipient uses a corresponding decryption key to revert it to its original form (known as plaintext). This process makes it extremely difficult for hackers to understand the content, even if they manage to intercept it.
How Does Network Encryption Work?
To understand how network encryption works, it helps to break the process down into key steps:
- Secure Connection Establishment
Before any data can be transmitted securely, a connection must be established between the sender and receiver. This usually involves agreeing on a set of encryption protocols and initiating a handshake process.
- Key Exchange
The devices must securely exchange cryptographic keys without exposing them to external threats. Modern systems often use asymmetric encryption methods (like RSA) or key exchange algorithms (like Diffie-Hellman) to facilitate this.
- Data Encryption and Transmission
Once the keys are shared, data is encrypted using an algorithm (such as AES or ChaCha20). The encrypted packets are then transmitted over the network.
- Decryption and Validation
At the receiving end, the system uses the decryption key to revert the data back into its original, readable state. During this stage, it can also verify the integrity and authenticity of the data using hashes or digital signatures.
- Session Termination
After the secure communication session ends, temporary encryption keys are typically discarded to prevent reuse or compromise.
Throughout this process, popular encryption protocols like TLS (Transport Layer Security) or IPSec ensure that data remains confidential and tamper-proof during transit.
Why Is Network Encryption Important?
Encryption is no longer optional; it’s essential. Here’s why:
- Data Confidentiality
Sensitive information like login credentials, payment details, or health records must be kept private. Encryption ensures only the intended recipient can read the data.
- Data Integrity
Encryption often includes mechanisms to detect tampering. This ensures the data received is exactly what was sent, free from manipulation.
- Compliance Requirements
Regulations like GDPR, HIPAA, and PCI DSS require encryption as part of data protection strategies. Non-compliance can result in hefty penalties.
- User Trust
Indicators like the padlock icon in browsers (which signals HTTPS/TLS encryption) help build trust among users by showing that their connection is secure.
- Protection from Cyber Threats
Encryption defends against common threats such as man-in-the-middle attacks, packet sniffing, and data breaches.
Encryption in Action: Real-World Examples
Network encryption is widely used across many sectors:
- Financial Institutions protect online banking transactions with strong encryption to prevent fraud.
- Healthcare Providers encrypt patient records to comply with privacy laws and safeguard sensitive data.
- E-commerce Sites use HTTPS encryption to secure customer transactions and personal details.
- Government Agencies use encrypted communication channels for classified information.
In each of these scenarios, encryption is a critical layer in the defense system.
Best Practices for Secure Network Encryption
Organizations looking to implement strong network encryption should consider these strategies:
- MACsec Encryption
Encrypt data at the data link layer to protect internal communications within enterprise networks.
- Zero Local Access
Restrict local access (such as SSH or console) to reduce exposure to unauthorized control or tampering.
- Tamper-Proof Hardware
Use devices with security modules like TPM (Trusted Platform Module) to protect keys and certificates.
- 802.1X and SSO Authentication
Employ identity-based access controls to ensure only verified users and devices access the network.
- Guest Traffic Isolation
Separate guest traffic from internal systems using tunneling or VLAN segmentation.
- Certifications and Standards Compliance
Adhere to high-security standards such as ISO 27001 and SOC 2 to ensure encryption practices meet industry best practices.
Challenges in Network Encryption
Despite its strengths, encryption comes with challenges:
- Performance Overhead: Encrypting and decrypting data adds processing time, potentially impacting performance in real-time applications.
- Key Management: Storing, rotating, and revoking keys securely is complex and requires dedicated systems or personnel.
- Implementation Complexity: Poorly implemented encryption can create security gaps. Misconfigurations can lead to vulnerabilities, even if encryption is technically in place.
The Future of Network Encryption
The digital world is evolving rapidly, and so are encryption technologies. Looking ahead:
- Post-Quantum Cryptography is being developed to counteract the future threat of quantum computing, which could break current encryption methods.
- Automated Key Lifecycle Management will help reduce human error and enhance encryption governance.
- AI-Driven Security Systems may use encryption more intelligently, adapting based on real-time risk levels.
Organizations that stay ahead of these trends will be better equipped to handle emerging threats.
Conclusion
Network encryption is a foundational element of modern cybersecurity. As data flows faster and cyber threats become more sophisticated, protecting information in transit is more crucial than ever. Whether you’re a small business or a large enterprise, encryption helps ensure that your data remains private, secure, and trustworthy.
By embracing layered security practices and implementing encryption at various points in the network, organizations can confidently defend against evolving digital threats—and build lasting trust with their users.